
Data breach response strategies are critical in today’s digital landscape where organizations face increasing threats to their sensitive information. A well-crafted response plan not only mitigates damage but also helps maintain trust with customers and stakeholders. By understanding the key components of a data breach response, organizations can effectively navigate the complexities of incident management and emerge stronger.
As we delve deeper into this topic, we will explore the essential elements of an effective data breach response plan, including detection methods, legal compliance, and post-breach recovery strategies. With the right approach, organizations can enhance their security posture while ensuring they are prepared to act swiftly and decisively in the event of a data breach.
Data Breach Response Plan
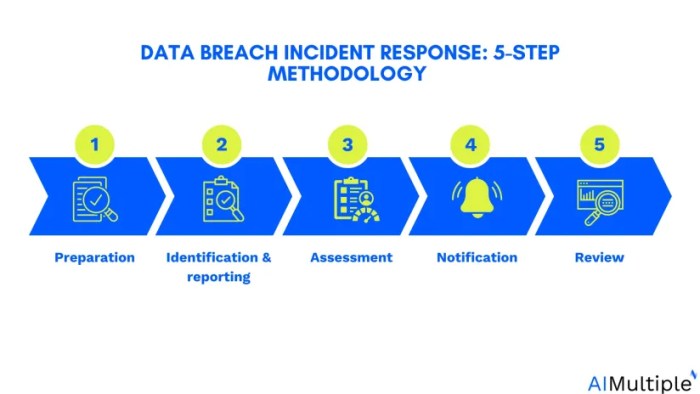
A comprehensive data breach response plan is essential for any organization to mitigate the impact of a breach effectively. This plan provides a structured approach to addressing security incidents, ensuring a swift and organized reaction that can protect sensitive information and maintain stakeholder trust. By establishing clear guidelines and a coordinated team effort, organizations can reduce the damage caused by data breaches and streamline recovery efforts.An effective data breach response plan typically includes several critical components that guide organizations in their response strategy.
These components not only help in identifying the breach but also in addressing its repercussions. Each element plays a pivotal role in ensuring that the organization can respond effectively and minimize risk to its data and reputation.
Essential Components of a Data Breach Response Plan
A well-structured data breach response plan consists of various essential components that work together to address the incident comprehensively. These components include:
- Preparation: Developing policies and procedures, training team members, and performing regular security assessments to anticipate potential breaches.
- Detection and Analysis: Implementing monitoring tools to detect unusual activities and analyzing the nature and extent of the breach quickly.
- Containment: Taking immediate steps to contain the breach to prevent further data loss, which may involve isolating affected systems.
- Eradication: Identifying and removing the root cause of the breach, which may involve patching vulnerabilities or improving security measures.
- Recovery: Restoring affected systems and data to normal operations while ensuring that no residual vulnerabilities remain.
- Post-Incident Review: Conducting a thorough analysis of the breach to learn from the incident and update the response plan accordingly.
Roles and Responsibilities of Team Members
The success of a data breach response plan relies heavily on the clear definition of roles and responsibilities within the response team. Assigning specific tasks ensures efficient communication and action during an incident. Key roles typically include:
- Incident Response Team Leader: Responsible for overseeing the response effort, coordinating team members, and serving as the primary contact for external stakeholders.
- IT Security Specialists: Focus on technical aspects such as breach detection, containment, and eradication, ensuring that systems are secured and vulnerabilities are addressed.
- Legal Counsel: Advises on legal obligations, compliance issues, and potential liabilities, ensuring that the organization adheres to laws and regulations.
- Public Relations Officer: Manages communication with the media and stakeholders, crafting messages that maintain public trust and transparency during the incident.
- Human Resources Representative: Addresses any employee-related issues that arise from the breach and ensures that staff are kept informed throughout the process.
Effective Communication Strategies During a Data Breach
Maintaining effective communication during a data breach is crucial to managing the incident and minimizing its impact. Clear and timely communication can prevent misinformation and confusion among stakeholders. The following strategies are important for effective communication:
- Internal Communication: Establish regular updates for employees regarding the breach, the steps being taken, and any changes in procedures.
- External Communication: Develop a comprehensive communication plan for stakeholders, including customers, partners, and the media, to provide accurate information and updates.
- Transparency: Be open about the nature of the breach, the data affected, and the measures being implemented to resolve the issue, which can help maintain trust.
- Feedback Mechanism: Encourage stakeholders to ask questions and express concerns, allowing the organization to address specific issues and provide reassurance.
- Post-Incident Reporting: After resolving the breach, provide a detailed report outlining what occurred, how it was handled, and the steps taken to prevent future incidents.
“An effective response to a data breach goes beyond recovery; it’s about restoring trust and ensuring robust security moving forward.”
Incident Detection and Analysis
Incident detection and analysis are critical components of an effective data breach response strategy. Organizations must be proactive in identifying potential breaches to minimize damages and protect sensitive information. By leveraging real-time detection methods and comprehensive analysis techniques, businesses can effectively mitigate risks and respond to incidents swiftly.
Methods for Real-Time Detection of Data Breaches
Real-time detection of data breaches involves monitoring systems and networks continually to identify unusual activities that may indicate a breach. The following methods are essential for effective detection:
- Intrusion Detection Systems (IDS): These systems analyze network traffic for suspicious activities and generate alerts when potential breaches occur. They can be host-based (monitoring individual devices) or network-based (monitoring the network as a whole).
- Security Information and Event Management (SIEM): SIEM solutions collect and analyze log data from various sources in real time, helping organizations detect patterns that may signify a breach.
- Anomaly Detection Algorithms: Using machine learning, these algorithms can identify deviations from normal behavior patterns, flagging potential security incidents as they occur.
- Endpoint Detection and Response (EDR): EDR tools continuously monitor end-user devices for malicious activities and provide incident response capabilities to contain breaches swiftly.
Techniques for Analyzing Breach Data
Analyzing breach data is crucial to understanding the extent and impact of a data breach. Effective techniques include:
- Log Analysis: Reviewing system and application logs to trace the breach’s timeline and identify how the intruder gained access.
- Data Correlation: Comparing data from various sources to connect disparate pieces of information, revealing a more comprehensive picture of the breach.
- Forensic Analysis: Conducting thorough examinations of compromised systems to recover lost data, understand the attack vector, and determine what information was accessed or stolen.
- Impact Assessment: Analyzing the potential consequences of the breach on business operations, customer trust, and regulatory compliance.
Tools and Software for Incident Detection and Analysis
Utilizing the right tools and software is essential for efficient incident detection and analysis. These solutions enhance visibility and streamline response efforts:
- Splunk: A powerful analytics platform that helps organizations monitor their IT infrastructure and detect anomalies in real-time.
- AlienVault: An integrated security management solution that includes IDS capabilities and threat intelligence to improve incident detection.
- IBM QRadar: A SIEM solution that provides advanced analytics to detect security breaches and prioritize responses based on risk.
- Wireshark: A network protocol analyzer that enables deep inspection of network traffic, assisting in the detection of unusual activities.
- Carbon Black: An EDR solution that provides real-time visibility and response capabilities to threats on endpoint devices.
“Timely incident detection and thorough analysis can significantly reduce the impact of data breaches, preserving organizational integrity and customer trust.”
Legal and Regulatory Compliance
With the increasing frequency and severity of data breaches, organizations must navigate a complex landscape of legal and regulatory requirements following such incidents. Compliance not only helps to mitigate legal risks but also fosters trust with clients and stakeholders. Understanding these obligations is essential for effective breach response and management.Organizations are obligated to adhere to various laws and regulations depending on their geographic location and the nature of the data they handle.
In many jurisdictions, failure to comply with these legal requirements can result in significant fines and damage to reputation. An essential component of compliance is the prompt reporting of incidents to relevant authorities, which not only fulfills legal obligations but also contributes to broader data protection efforts.
Legal Requirements After a Data Breach
Organizations must be aware of specific legal requirements that come into play after a data breach. These typically include:
Notification Obligations
Many jurisdictions require organizations to notify affected individuals and regulatory authorities within a specific timeframe. For instance, the General Data Protection Regulation (GDPR) mandates notification within 72 hours of becoming aware of a breach.
Data Protection Impact Assessments (DPIA)
Depending on the severity and nature of the breach, organizations may be required to conduct a DPIA to evaluate risks and mitigate the impact.
Documentation and Record-Keeping
Organizations should document the breach, including the nature of the data involved, the number of individuals affected, and the steps taken in response. This documentation is crucial for compliance checks and potential investigations.
Coordination with Law Enforcement
In certain cases, particularly those involving criminal activity, it is necessary to involve law enforcement. This can help in recovering data and preventing future breaches.
Incident Reporting to Relevant Authorities
Prompt incident reporting is a critical aspect of legal compliance following a data breach. The importance of timely reporting cannot be overstated. Here are key points regarding incident reporting:
Minimizing Legal Consequences
Timely reporting can significantly reduce the legal repercussions for organizations, as proactive measures are often viewed positively by regulators.
Facilitating Investigations
Reporting to authorities enables them to take necessary actions, such as investigating patterns of attacks and offering guidance to other organizations.
Public Trust
Transparency in reporting fosters trust among customers and stakeholders, demonstrating that the organization takes data protection seriously.
Compliance Checklist for Data Protection Laws and Regulations
To ensure compliance with data protection laws following a data breach, organizations can utilize the following checklist. This list serves as a guide to verify that all legal obligations are met:
Assess the Breach
Determine the scope, nature, and impact of the breach; identify the data compromised.
Notify Affected Individuals
Inform individuals whose data has been compromised, providing them with information on protective measures.
Report to Authorities
File necessary reports with appropriate regulatory bodies, adhering to established timelines.
Conduct a DPIA
If required, evaluate the risks associated with the breach and document findings.
Review Security Measures
Analyze existing security protocols and address any vulnerabilities that led to the breach.
Maintain Documentation
Keep detailed records of the breach, all communications, and actions taken in response.
Train Employees
Ensure that all staff are aware of updated policies and procedures regarding data protection and breach response.
Evaluate and Improve Processes
After addressing the immediate concerns, assess the response plan’s effectiveness and implement improvements for future incidents.
“Proactive compliance not only mitigates risks but also reinforces an organization’s commitment to protecting sensitive data.”
Post-Breach Activities
After a data breach, organizations must follow a structured approach to address the aftermath effectively. Post-breach activities are crucial for assessing the damage, learning from the incident, and restoring trust with affected stakeholders. This phase not only involves damage control but also lays the groundwork for enhancing future incident response strategies.
Framework for Post-Breach Review
Conducting a thorough post-breach review helps organizations understand what went wrong and how to improve future responses. A structured framework can include the following steps:
- Gather the Response Team: Assemble the incident response team and relevant stakeholders to discuss the breach and its impact.
- Document the Incident: Create a comprehensive report that Artikels the timeline of the breach, the response actions taken, and the effectiveness of those actions.
- Identify Gaps in the Response: Analyze the response process to identify weaknesses and areas for improvement. This can include evaluating communication, detection, and mitigation strategies.
- Update Policies and Procedures: Adjust existing policies based on findings from the review to ensure better preparedness for future incidents.
- Conduct Training Sessions: Implement training programs for staff to reinforce the importance of data security and the lessons learned from the breach.
Restoring Customer Trust
Restoring trust after a data breach is essential for maintaining customer relationships and brand reputation. Organizations can adopt several strategies to reassure affected customers:
- Transparent Communication: Inform customers about what happened, how it affects them, and the steps being taken to rectify the situation. Transparency builds trust.
- Offer Support: Provide resources such as credit monitoring services or identity theft insurance to affected individuals to show that the organization cares about their wellbeing.
- Enhance Security Measures: Publicly share improvements made to security protocols as a direct response to the breach, demonstrating a commitment to protecting customer data.
- Engage With Customers: Create forums or discussion platforms where customers can voice their concerns and receive answers directly from the organization.
Ongoing Surveillance and Vulnerability Assessments
After a breach, continuous monitoring and assessment are vital for identifying potential vulnerabilities and preventing future incidents. Effective methods include:
- Implementing Continuous Monitoring Tools: Utilize advanced security tools that provide real-time monitoring and alerts for suspicious activities.
- Regular Vulnerability Assessments: Schedule periodic assessments to identify and remediate security weaknesses proactively.
- Penetration Testing: Conduct simulated attacks to evaluate the effectiveness of security controls and uncover potential entry points for malicious actors.
- Updating Software and Systems: Ensure that all systems are regularly updated with the latest security patches to close vulnerabilities that can be exploited.
Integration with Digital Marketing Strategies
Incorporating data breach response strategies into digital marketing is crucial for maintaining brand integrity and consumer trust. As digital platforms grow, so do the risks associated with data breaches. It’s essential to ensure that marketing efforts are not only effective but also secure. This integration can help organizations navigate the complexities of digital engagement while protecting sensitive information.
Incorporating Data Breach Response into Search Engine Marketing
Search engine marketing (SEM) is an essential tool for online visibility, and having a robust data breach response plan can enhance credibility. When a breach occurs, it can significantly affect online reputation and search rankings. Here are key strategies:
Transparency in Communication
Clearly communicate any data breach incidents in your marketing campaigns. This demonstrates accountability and can improve trust among customers. Use -optimized press releases to reach wider audiences.
Update s
Adapt your strategy to include terms related to security and privacy. Consumers are increasingly searching for secure brands, so integrating these s can improve visibility.
Content Creation
Produce content that educates consumers on how you protect their data. Blog posts, infographics, and FAQs about data security can enhance your relevance in searches tied to privacy.
Utilize Remarketing
After a breach, use remarketing strategies to reassure previous visitors about your enhanced security measures. This can help in regaining trust and encourage repeat visits to your site.
Implications of a Data Breach on Social Media Marketing
A data breach can severely impact social media marketing efforts, as trust and reputation are critical on these platforms. When a breach occurs, it’s vital to respond swiftly. Here’s how to manage the implications effectively:
Crisis Management
Develop a clear crisis communication plan that includes social media protocols. This should Artikel when and how to address the breach with your audience.
Engagement Tactics
Actively engage with your audience by addressing their concerns directly on social media. Use direct messaging for sensitive issues and public posts for general updates.
Content Adjustment
Modify your content strategy to include posts about your commitment to data security. Share tips on how customers can protect their information and highlight any new security measures you’ve implemented.
Monitor Brand Sentiment
Use social listening tools to track brand sentiment and address negative feedback promptly. This proactive approach can mitigate damage and restore trust.
Promoting Enhanced Security Measures in Video Marketing Content
Video marketing is a powerful tool for conveying messages effectively. Promoting enhanced security measures through video can help reassure customers and strengthen brand loyalty. Here’s a structured plan to implement this:
1. Create Informative Videos
Develop videos that explain your security measures and how they protect customer data. Use clear visuals and straightforward language to make the content accessible.
2. Share Customer Testimonials
Feature testimonials from customers praising your commitment to security. Authentic experiences can enhance credibility and trust.
3. Utilize Live Q&A Sessions
Host live sessions on platforms like YouTube or Instagram where customers can ask questions about data security. This interactive format can humanize your brand and clarify concerns in real-time.
4. Incorporate Security Tips
Regularly include segments in your marketing videos that educate viewers on best practices for online security. This positions your brand as a thought leader in data protection.By strategically integrating data breach response strategies into digital marketing, businesses can not only mitigate the fallout from breaches but also enhance their overall marketing effectiveness.
Enhancing Online Security Measures
In the digital age, securing online assets has become a top priority for businesses of all sizes. A robust online security strategy not only protects sensitive data but also fosters trust among customers. This section focuses on best practices for securing web hosting services, implementing effective spam blockers, and making web design choices that enhance overall security.
Securing Web Hosting Services
Selecting a reliable web hosting service is fundamental for maintaining online security. Businesses should ensure that their chosen provider offers comprehensive security features. The following practices can help in securing web hosting services against breaches:
- Use Secure Hosting Providers: Choose providers that offer SSL certificates, firewalls, and DDoS protection.
- Regular Software Updates: Ensure that the server’s operating system, web applications, and plugins are updated frequently to address vulnerabilities.
- Implement Strong Authentication: Use SSH keys or other secure methods for accessing servers, rather than relying on simple passwords.
- Backup Data Regularly: Maintain up-to-date backups to recover quickly in case of a breach.
- Monitor Server Activity: Regularly check logs for suspicious activities or unauthorized access attempts.
Implementing Spam Blockers
Spam emails are not just an annoyance; they can also serve as vectors for phishing attacks and malware. Implementing effective spam blockers is crucial for protecting sensitive information. Here are guidelines for deploying spam blockers:
- Utilize Reputable Spam Filters: Invest in high-quality spam filtering solutions that utilize machine learning to adapt to new threats.
- Configure Email Authentication Protocols: Set up SPF, DKIM, and DMARC to verify sender authenticity and reduce phishing risks.
- Regularly Update Filters: Keep spam filters updated with the latest threat definitions to catch emerging spam tactics.
- User Education: Train employees to recognize spam and report suspicious emails to reduce the risk of falling victim to attacks.
Web Design Choices for Enhanced Security
The design of a website can significantly influence its security posture. Thoughtful design choices can mitigate risks and enhance user trust. Key considerations include:
- Responsive Design: Ensure that the website is mobile-friendly to avoid vulnerabilities associated with outdated mobile interfaces.
- Minimalist Approach: Limit the use of third-party plugins and scripts that may introduce security holes.
- Secure User Input: Utilize input validation and sanitization techniques to protect against injection attacks.
- Visible Security Features: Display security badges and SSL indicators to reassure users about the safety of their transactions.
“A secure website is not just about technology; it’s about fostering confidence and trust.”
Building Community Awareness
Creating awareness within the community is crucial for fostering a culture of security that can significantly mitigate the impact of data breaches. As technology evolves, so does the complexity of cyber threats, making it imperative for communities to stay informed and educated. Engaging the public through various platforms can enhance their understanding of data breaches and empower them to take proactive steps towards safeguarding their personal information.
Using Social Networking Platforms to Educate the Public
Social networking platforms like Facebook, Twitter, and Instagram are powerful tools for disseminating information about data breaches and preventative measures. These platforms allow organizations to reach a broad audience quickly and effectively. Engaging content such as infographics, bite-sized tips, and interactive posts can be leveraged to educate users about recognizing potential threats and the importance of online security.
- Infographics: Visually appealing graphics can simplify complex information about data breaches and security practices, making it easier for the audience to grasp key concepts.
- Live Q&A Sessions: Hosting live sessions where experts answer security-related questions can increase engagement and provide direct support to community members.
- Regular Updates: Consistently updating followers about the latest threats and breaches ensures that the community remains informed and vigilant.
Campaign for Promoting Internet Security Awareness through Social Bookmarking
A strategic campaign utilizing social bookmarking sites can effectively promote internet security awareness. By creating dedicated pages on platforms like Pinterest or Delicious, organizations can curate and share valuable resources related to data breach prevention. This approach not only educates users but also encourages them to share these resources within their networks.
- Resource Curation: Compiling a list of articles, tools, and tips about data privacy and security can serve as a valuable reference for users.
- Challenges and Contests: Engaging the community through challenges, such as sharing the most effective security tips, can boost participation and spread awareness.
- Collaborations: Partnering with influencers or organizations in the tech space can amplify the reach of the campaign and provide credibility.
The Role of Video Streaming in Sharing Information on Data Breach Prevention
Video streaming platforms like YouTube and Twitch have the potential to be instrumental in educating the public about data breach prevention. Video content can capture attention and engage audiences more effectively than traditional text-based resources.
- Tutorial Videos: Creating step-by-step guides on setting up security measures, such as two-factor authentication or password managers, can empower viewers to take action.
- Webinars: Hosting informative webinars featuring industry experts can provide valuable insights into the latest security trends and solutions.
- Storytelling: Sharing real-life stories of individuals or businesses affected by data breaches can humanize the issue and highlight the importance of proactive measures.
Concluding Remarks

In conclusion, having robust data breach response strategies is not just a necessity but a strategic advantage in safeguarding your organization. By implementing a comprehensive plan that encompasses detection, compliance, and recovery, businesses can not only protect their data but also reassure clients and partners of their commitment to security. As threats continue to evolve, staying informed and prepared is the key to navigating the complexities of data breaches confidently.
Question Bank
What should be the first step after a data breach?
The first step is to contain the breach and prevent further unauthorized access to data.
How often should organizations review their response plan?
Organizations should review their response plan at least annually or after any significant incident.
What legal obligations do organizations have after a breach?
Organizations must notify affected individuals and regulatory authorities as per applicable data protection laws.
Can training help prevent data breaches?
Yes, regular training for employees on security best practices can greatly reduce the risk of breaches.
How can organizations rebuild trust after a breach?
Transparency about the breach, timely communication, and improved security measures can help restore trust.





